In this week’s digest, we’ll cover:
- Linux NetFilter Kernel Use After Free Vulnerability
- WordPress Core v6.2 XSS/CSRF/Directory Traversal Vulnerability
- Linux OverlayFS Vulnerability
CVE-2023-32233: Linux NetFilter kernel vulnerability
Background
NetFilter is a packet filtering and network address translation framework built into the Linux kernel to manage network traffic. This is controlled by userspace utilities such as iptables, UFW and nft. Both iptables and nftables are based on NetFilter, with nftables being the newer implementation. System administrators use these tools to configure local firewall rules and monitor network traffic.
Vulnerability
Vulnerabilities are tracked as CVE-2023-32233, is a use-after-free vulnerability in the ‘nf_tables’ module of NetFilter. “nf_tables” is enabled by default on most Linux operating systems. “Nf_tables” accepts invalid configurations, causing problems in some scenarios when invalid batch operations are performed. If invalid batch operations are crafted in certain ways, they can lead to internal state corruption within the Linux kernel. This happens because the ‘nf_tables’ module does not properly handle anonymous sets (sets of unnamed types for which identifiers are assigned by the kernel).
A corrupted state can be exploited to perform arbitrary reads and writes to kernel space memory. This can be used to elevate the privileges of local users. All versions of the Linux kernel prior to version 6.3.1 are vulnerable to this exploit.
Note that an attacker would need access to an established Linux system before attempting to exploit this vulnerability. Additionally, he needs CAP_NET_ADMIN privileges and the ability to work directly with NetFilter via a 3rd party API.
The impact of this vulnerability is significant because it affects modules that are enabled by default on many Linux operating systems. Additionally, a proof of concept has been released. This increases the chances of this vulnerability being exploited in the wild.
relief
- We strongly recommend updating the Linux kernel on your system to version 6.3.2 or later.
- Disable Unprivileged User Namespace
WordPress Core v6.2 XSS/CSRF/Directory Traversal Vulnerability
Background
WordPress consists of multiple parts: core, database, themes and plugins. WordPress Core is the foundation for the rest of the WordPress platform and enables all administrative functions.
Vulnerability
WordPress Core v6.2 has several vulnerabilities that we will cover.
CVE-2023-2745: directory traversal
This vulnerability is tracked as CVE-2023-2745, allowing an attacker to abuse the ‘wp_lang’ parameter to perform directory traversal on a WordPress site. An attacker could access and load arbitrary language translation files. Additionally, if an attacker has sufficient access to upload translation files, this vulnerability can also be used to perform cross-site scripting.
CVE Pending: Cross-Site Request Forgery (CSRF)
This vulnerability, which does not have a CVE ID at the time of writing, is caused by a lack of nonce validation in AJAX functions. Her AJAX function called “wp_ajax_set_attachment_thumbnail” allows unauthenticated users to update the file associated with the attachment thumbnail. This only happens when an authenticated user performs an action such as clicking a link.
WordPress has determined that exploitation of this vulnerability is unlikely in the wild, as exploitation requires a complex sequence of events.
CVE Pending: Cross-Site Scripting (XSS)
This vulnerability, which does not have a CVE ID at the time of writing, is due to improper protocol validation when processing responses from oEmbed Discovery. oEmbed is a WordPress format type that allows the rendering of URLs from third-party sites. Typically this is used when a user links to another site in a comment and a preview of the linked site is shown. An attacker with Contributor or higher privileges could craft a malicious oEmbed payload of her with a third-party URL to cause arbitrary script to run when a user visits that third-party URL.
Note: The original patch for these vulnerabilities, version 6.2.1, also fixes minor shortcode vulnerabilities. A shortcode vulnerability fix broke functionality. Version 6.2.2 fixes this issue.
relief
- We highly recommend updating WordPress to version 6.2.2 or later.
CVE-2023-0386: OverlayFS Vulnerability
Background
SetUID is a special file permission that allows any user with execute permission to execute a binary as the user or group that owns the file. If a binary owned by root has her SetUID bit set, a user with execute permissions can run it as root.
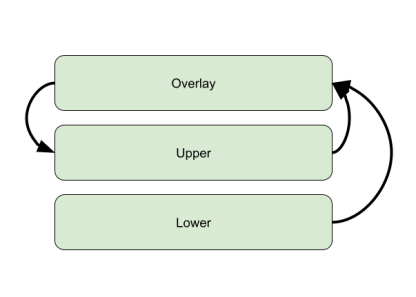
OverlayFS is a method of merging multiple mount points on a Linux file system into one integrated file system. It consists of multiple layers: lower layer, upper layer and overlay.
- The “lower” layer contains the base mount points for existing data. Data can be accessed upstream in the overlay layer.
- The “upper” layer is defined as part of the overlay filesystem. All files written to the overlay layer are copied to the upper layer. When the file is modified in the lower layers, the changes are propagated to the overlay layer and then to the upper layers.
- The “overlay” layer is the top layer of the filesystem. It consists of upper-layer and lower-layer files. All files are accessible from the overlay layer.
Here’s a simple diagram showing how file changes are propagated through OverlayFS.
Vulnerability
This vulnerability is tracked as CVE-2023-0386, all versions of the Linux kernel prior to 6.2-rc6 are vulnerable. When adding files to the OverlayFS filesystem, the overlay layer does not properly check the validity of users/groups in the current namespace before copying them to upper layers. An attacker can add a binary with the SUID bit set to a lower layer and force it to be copied to a higher layer.
An attacker could create a new virtual filesystem and namespace, generate a SUID binary with root ownership, and mount it to the OverlayFS filesystem. The OverlayFS filesystem does not check if user/group ownership is valid in the current namespace and copies binaries with permissions intact. An attacker can then execute her SUID binary from a higher layer and elevate her privileges.
relief
- We strongly recommend updating the Linux kernel on your system to the latest version.
- Disable unprivileged user namespaces.

